Encrypt Your Internet Connection for as Little as $3/mo with PIA VPN Learn more
Disclaimer: This content is intended to be consumed by cyber security professionals, ethical hackers, and penetration testers. Any attacks performed in this video should only be performed in environments that you control or have explicit permission to perform them on.
This post is a continuation from my last regarding cracking encrypted .zip archives. But what happens if you come across an encrypted 7zip archive? The 7-Zip encryption is actually quite good and can require a lot of time to bruteforce, but this guide will show you how weak passwords can still break good encryption.
I’ll use LightWeight from HackTheBox as an example for this guide. Please note that this post does not intend to serve as a walkthrough for the box.
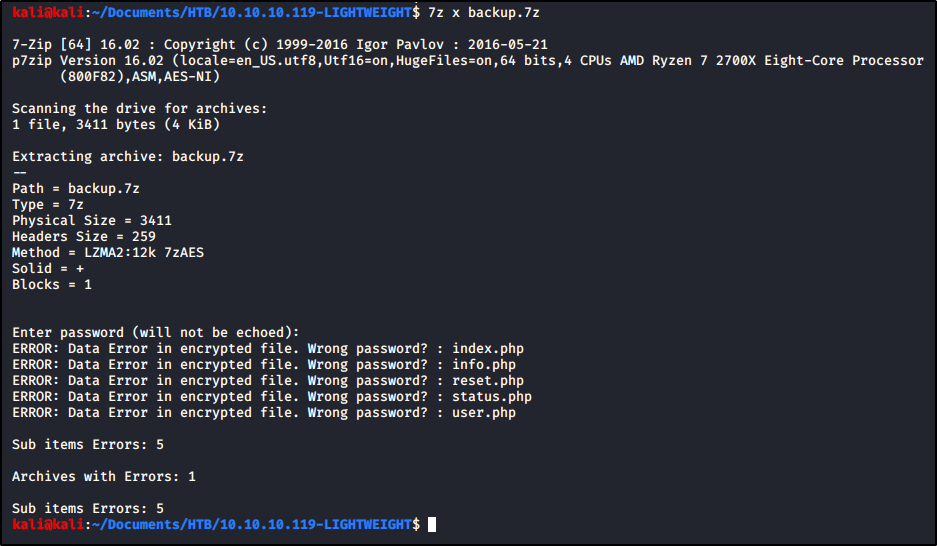
To begin, we already have the archive we wish to crack on our filesystem. Our goal is to crack the file named backup.7z.

We try to open the archive using 7z, but we’re prompted for a password that we do not know. When prompted, I entered password in the example below, but that did not work.
7z x backup.7z
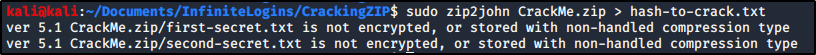
We can start by using zip2john, but we find that the tool is unable to obtain the hash.

To proceed, we’ll need a tool called 7z2john. If you get an error when trying to run this tool, you may need to install the following package.
sudo apt install libcompress-raw-lzma-perl -y
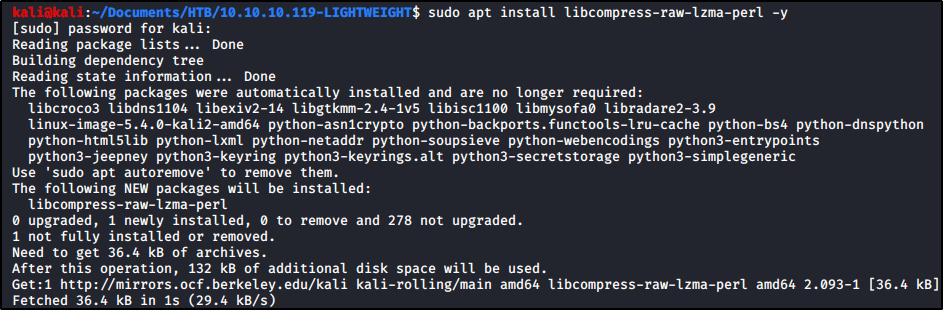
With that package installed, let’s locate 7z2john and copy the full path.
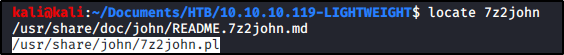
Now let’s run this tool against backup.7z.
/usr/share/john/7z2john.pl backup.7z

Nice! We’ve extracted the hash. I’m just going to rerun the command again and output the results into a file named lightweight7z.hash
/usr/share/john/7z2john.pl backup.7z > lightweight7z.hash
Now let’s vi the file so we can remove the first bit. With the cursor at the top, I’m going to enter 10x while still in command mode so that I delete the first 10 characters. We should be left with only the hash now. To write my changes and quit, I’ll enter :wq

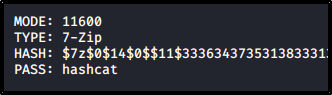
With the hash in hand, we’re ready to pass the hard work over to hashcat. First, we need to identify what numeric value hashcat assigns to 7-zip archives. Let’s run hashcat --example-hashes and search the results for 7-Zip. We find that we’ll need mode 11600
As long as you have a wordlist ready, let’s throw this at hashcat!
hashcat -m 11600 lightweight7z.hash /usr/share/wordlists/rockyou.txt

After some time, we see that our password is cracked. The credential appears to be delete.
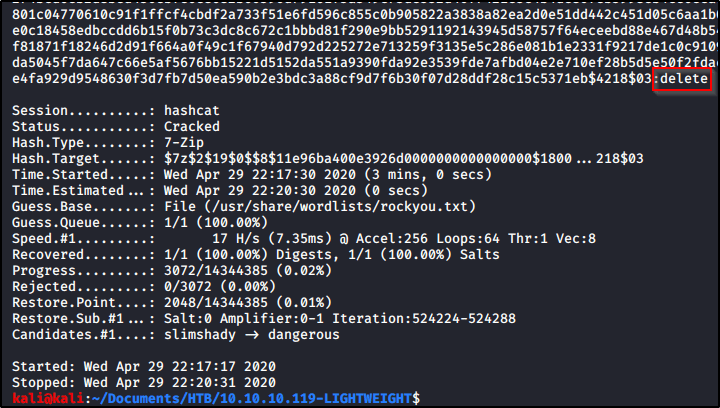
Let’s test this by running 7z x backup.7z again, but entering delete when prompted for the credential.

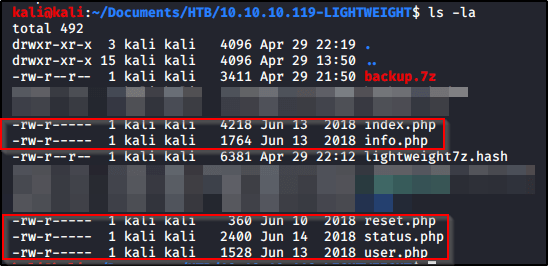
Now we see the archived .php files available to us in our present working directory!
That’s it! Super quick and easy to crack this if you have a weak password. While the 7-zip encryption is actually quite good and can make a password very difficult to crack, weak passwords will end up harming you in the end.