Encrypt and Anonymize Your Internet Connection for as Little as $3/mo with PIA VPN. Learn More
Have you ever encountered the following error within Gobuster?
Error: the server returns a status code that matches the provided options for non existing urls. http://ipaddress/9b9353c0-3de2-4df5-abd7-0f618e4d70ab => 200. To force processing of Wildcard responses, specify the ‘–wildcard’ switch
Likely, the webserver you’re attacking is configured to always respond with a 200 response code. For example, let’s look at BART on Hack The Box.

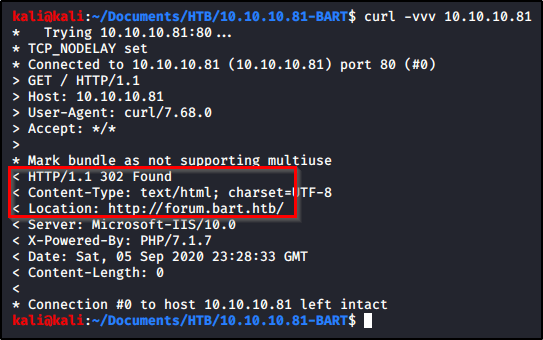
Let’s see if we can extract anything with Curl. We’ll start by sending a request out to the default page. We see that it returns a 302 redirect to forum.bart.htb.
curl -vvv 10.10.10.81
Let’s try a request to a page we know doesn’t exist, and we are returned a success 200 message that displays an image. This explains why Gobuster was returning a 200 message on each directory.

We can confirm this by browsing to the page and looking at the image.

Armed with this information, we know that 200 response codes are bad, but other response codes (such as a 302) indicate a directory is present. Let’s rerun our Gobuster command, but we’ll specify which response codes we want returned.
Checking the help page, we can see that Gobuster accepts the following response codes; “200,204,301,302,307,401,403”.
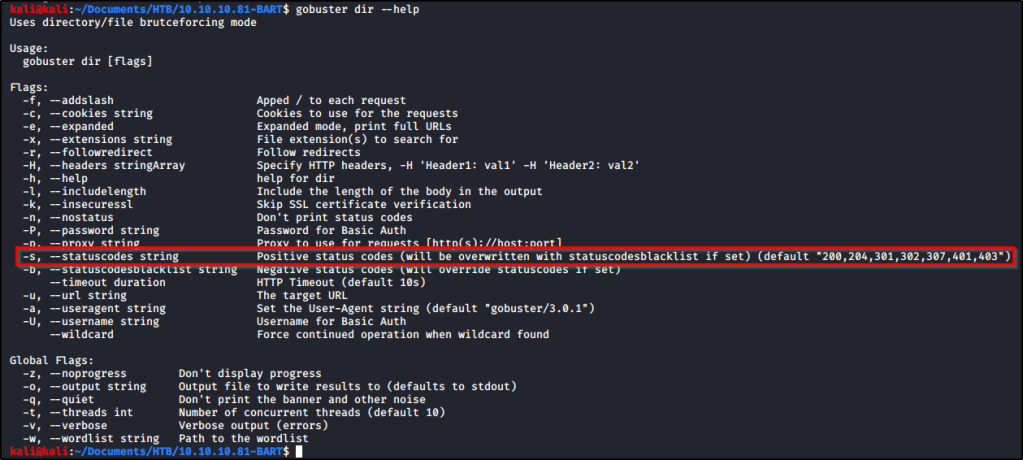
So our command will look like this.
gobuster dir -u http://10.10.10.81 -w /usr/share/dirbuster/wordlists/directory-list-lowercase-2.3-medium.txt -s "204,301,302,307,401,403"
And with that command running, we eventually start to get some real results back.
