This post intends to provide a list of helpful commands and tools that you can use when enumerating Port 389 on a machine. This list is far from exhaustive and will be updated as time progresses.
Let’s start by performing a search with simple authentication:
ldapsearch -h <targetIP> -x
If you get results back, let’s run the following command to try and get additional details out.
ldapsearch -h <targetIP> -x -s base namingcontexts
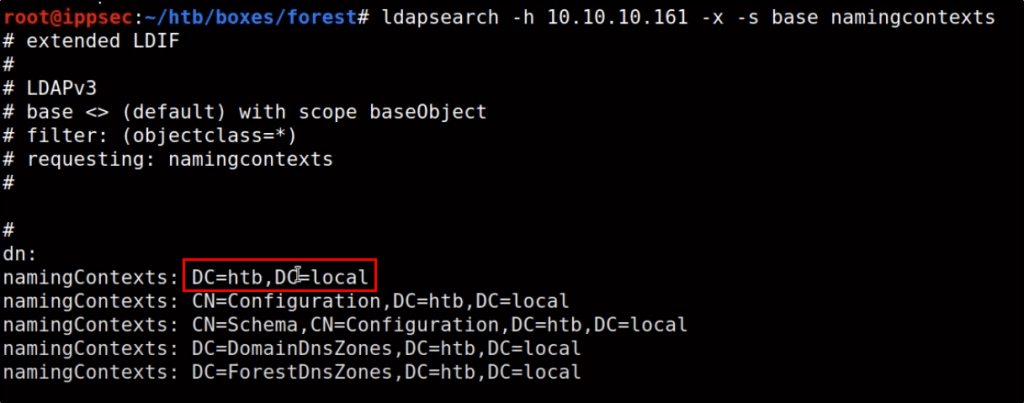
Based on the results, you’ll want to extract details about the primary Domain Component. For example, based on the above output, our next command would look like this.
ldapsearch -h <targetIP> -x -b "DC=htb,DC=local"
This should output a ton of information that you can then redirect to a file. If you do redirect to a file, the following commands may be helpful for extracting specific details.
cat ldap-anonymous.out | grep -i CN=
cat ldap-anonymous.out | grep -i member
cat ldap-anonymous.out | grep -i memberof
cat ldap-anonymous.out | grep -i user
Applying Filters to Queries
If you wanted to query LDAP directly, you can do so by adding your query to the end of your ldapsearch command. For example, we can find details of objects that have a class of “Person” by running the following command:
ldapsearch -h <targetIP> -x -b "DC=htb,DC=local" '(objectClass=Person)'
We can also just extract specific details about those that have a class of Person. For example, we could extract just the SAMAccountName and type.
ldapsearch -h <targetIP> -x -b "DC=htb,DC=local" '(objectClass=Person)' sAMAccountName sAMAccountType
Using this method is a great way to create a list of users that you can then use for Password Spraying attacks.