In early July of 2021, I decided to take on TCM Security’s new PNPT certification and passed it on my first attempt! This post intends to serve as a review of my experience, as well as help answer some of the common questions that I’ve seen online regarding the exam.

What is the PNPT?
The exam begins with external enumeration and some OSINT in order to get your initial foothold. Once you have that, you’ll pivot inside the environment with the ultimate goal being to compromise a domain controller and set up some sort of persistence.
There are a number of machines in the internal network, and you’ll need to compromise each one of them before you’re able to make it to the end objective. To do this, you’ll need to know techniques for Active Directory enumeration, exploitation, lateral movement, and some privilege escalation.
There are no limitations on tools (including LinPEAS and Metasploit). Five day time limit to hack, with an extra two days to write and submit your report. The exam is not proctored and getting going is as simple as paying for the exam and getting it scheduled.
If you fail, you will get a 2nd attempt for free.
My Background.
Let’s take a step back so I can share who I am and what knowledge I had going into the PNPT. As a teen, I knew I wanted to become an ethical hacker and eventually explore the world of Pentesting. I graduated with an associates degree (2yr) in Cyber Security & Networking in 2016, but that really didn’t mean much since I finished that program with zero certifications. Really, it gave me the baseline understanding of security, networking, and computer concepts – enough to get me started in IT.
As soon as I graduated, I started working help desk for a small MSP. Before long, I became the lead technician there, an IT Manager, and helped hire and mentor every technician that we brought on to our team. Doing that for four years helped me learn a lot about Systems Administration, TCP/IP Networking, Office 365, Active Directory, PowerShell, etc. This job was great, but it wasn’t Pentesting – and I started to lose hope that I would ever make my dream a reality.
2019 is when that changed. I went to Defcon for the first time and really started to get involved with the Infosec community. When I got back home, I came across Heath Adams’ (the Founder of TCM Security) YouTube channel through his free 14hr “Zero to Hero” Ethical Hacking Course. The content on his channel helped me realize that becoming a Pentester is possible – you just have to put in the work.
Through his encouragement, I started down the OSCP path before 2019 was over, and unfortunately have been on it ever since. Countless hours of learning, and over $2,000 later, here I am in 2021 getting ready to take on the OSCP exam for the 5th time.
While I still haven’t earned the OSCP certification yet, I have definitely picked up a ton of skills along the way. I have since started Pentesting full time, and now help companies find vulnerabilities within their infrastructure, networks, and web applications. I have been doing this for a little over a year as of writing this post.
Why I Chose the PNPT
In late April, TCM Security announced the PNPT certification. By this point in time, I had already felt comfortable performing external and internal network penetration tests for real live companies, so taking on the PNPT was really only something I was interested in doing for two reasons:
- To support TCM Security. In many ways, I have always credited TCM Security with giving me the confidence to take the leap, quit my job, and get into Pentesting to begin with. Creating a new certification and taking on the big dogs is no small task, so I wanted to show my support for what they are doing as I know there are others out there that are in a similar situation as I was. Educational content that is easy to understand and affordable is something that this industry needs more of.
- To accredit my skills and give myself a boost of confidence. Failing the OSCP as many times as I have definitely doesn’t help with the rampant imposter syndrome that many folks in our community deal with day to day, and I really needed to prove to myself that I know what I’m doing. I had hoped the PNPT would help me verify that – and let me tell you, it really did.
My Exam Experience.
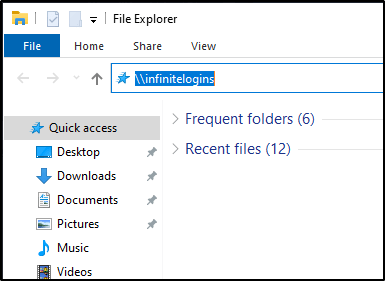
Let’s get down to the exam. The exam process is pretty straightforward and much like what you would expect if you were subcontracted on for a Pentest. You schedule a time for the engagement, that time comes around, and then you’re sent the Engagement Letter that contains the scope, limitations, and objectives. There will also be a VPN pack that you’ll use to connect to the environment and get to hackin’!
I decided to schedule my exam over the fourth of July holiday break since I had Monday off. I started my exam after work on Friday and was able to finish early Sunday afternoon – so roughly after 48 hours. I took the rest of Sunday to write up the report and actually received a reply later that same night, even though it was a US holiday. The 15 minute debrief call was scheduled for the next day, and I was told by the end of that call that I had passed!
I really enjoyed that the exam felt structured in a way where you’re able to make steady progress all the way through. While there are many rabbit holes, the exam felt architected so that you could tell whether or not you were on the right path and it seemed pretty clear that you would have to complete one objective before being able to move on to the next.
Ratings on Various Exam Aspects.
Note: Please keep in mind that these are my opinions as of time of writing. Because of this, these are subject to change in the future and do not represent the opinion of others.
Affordability – 10/10. Out of everything out there, I have not found another course/exam combo that can compete with the price offered by TCM Security. As of when I’m writing this post, the cost for the PNPT exam is $299, with various offers to get all of the training needed to pass for less than $100.
Course materials – 10/10. It’s refreshing to go through an exam where the course materials provided to you are sufficient for being able to pass the exam. For other exams in the industry, such as OSCP, it is common to have to pay an expensive amount for the course materials, and then fork out additional money for supplement materials in order to pass. In my experience, the materials offered by TCM Security Academy is sufficient to be able to pass the exam, with 80% of the necessary material being taught in the Practical Ethical Hacking (PEH) course.
Practicality – 10/10. As the name of the certification suggests, this exam is 100% practical. No multiple choice questions, no true or false – just you, computer systems, and your skills.
Lack of Stress – 8/10. Since you have 5 days before you have to worry about the report, there really isn’t a lot of pressure on this – especially compared to exams like the OSCP, where you only have 24 hours for exploitation. This exam also is not proctored, which can be seen as both a good and a bad thing. Considering there aren’t tool limitations in this exam, proctoring would only really be useful to try and validate your identity so that others don’t take the exam on your behalf. But in the end, you’re really just cheating yourself if you were to do something like that.
Realism – 7/10. There are many components of the exam that are realistic, but there are definitely items of the exam that are not realistic. For example, it never really felt like I was on actual corporate machines. The software installed on the various systems didn’t really make sense, especially when you correlate the job position of the user and the software on the systems. They also sprinkled in comedic bits throughout the exam, which I actually enjoyed quite a bit, but it does remind you that you’re in a fake environment and takes away from the “Real World” feel.
Difficulty – 6.5/10. During the exam, it is easy to feel pressure and get stuck. While I wouldn’t consider this exam difficulty “Advanced”, it was definitely challenging at times and you will find your emotions rising if you let them. Just remember that there are five days to complete this, which helps alleviate some of the pressure and puts things into perspective. You will also need to think a bit “outside the box” at times. You can’t just copy the course materials verbatim to get some attacks to work, rather, you’ll need to understand why the attack works and be able to apply critical thinking in order to successfully exploit them.
Recognition / Credibility – 3/10. This is, without a doubt, the number one drawback of taking the PNPT. As of today, the vast majority of organizations do not know what the PNPT is, nor what skillset it teaches. It is not currently recognizable by majority of HR departments, and likely not recognizable by many hiring managers in Infosec. This is not due to lack of the certification being worth anything, rather just a lack of time and exposure of the certification in the market. While holding this certification will definitely help you explain your skills within a job interview, I do feel like it will take some time before this certification will help you get passed the HR department on it’s own.
PNPT vs OSCP
This conversation could be its own independent post. In short, the OSCP and the PNPT are two very different exams with different requirements, different skillsets, and different objectives. They each hold a place in the market and I find them both valuable for various reasons.
While I do wish certain things about the OSCP and Offensive Security’s business practices were different, I cannot argue against the fact that the OSCP certification process is an extremely valuable experience for anybody getting into the world of Ethical Hacking. I would not be where I am today if it wasn’t for the OSCP journey.
With that said, the OSCP is not real-world realistic. It puts limitations on tools, sets an unrealistic timeframes, and uses unrealistic machines during the exam. The OSCP feels very much like a game in the sense that you’re only looking to pop shells while jumping through hoops – something that an organization doesn’t necessarily care about during a Pentest as long as you help them identify their most critical vulnerabilities.
Again, I could share a lot more on this topic – let me know if this is something you’d want to see.
Additional Tips
Remember the basics. It is easy to overthink things as you go into the exam. Just remember what you’ve learned and hold onto the basics. What is a reverse shell? What is a bind shell? 32bit vs 64bit executables. Common misconfigurations. Basics of enumerating common services. Etc.
Take breaks. This is a common suggestion for any practical exam in the Pentesting space, and it really is something that you must be doing. Don’t bang your head against the wall trying the same thing over and over – make sure to take breaks. Sometimes stepping away and coming back will help you find the item you’ve been missing.
Stay calm. This is a low pressure exam with plenty of time. If you’re ready to pass, you will know. If you’re not, well.. that takes us to my next tip.
Understand that failure is okay. TCM provides a free retake on their exam. Heath told me that only about 40% of their partipants pass on their first attempt, but majority make it on their 2nd. Failing doesn’t make you a loser – quitting does. Get back up, give it another shot, you’ll make it.