When on an engagement, it is common to need a custom wordlists for either Password Spraying, or Password Cracking when you have captured some hashes. This post intends to serve as a quick guide for leveraging Hashcat rules to help you build effective custom wordlists.
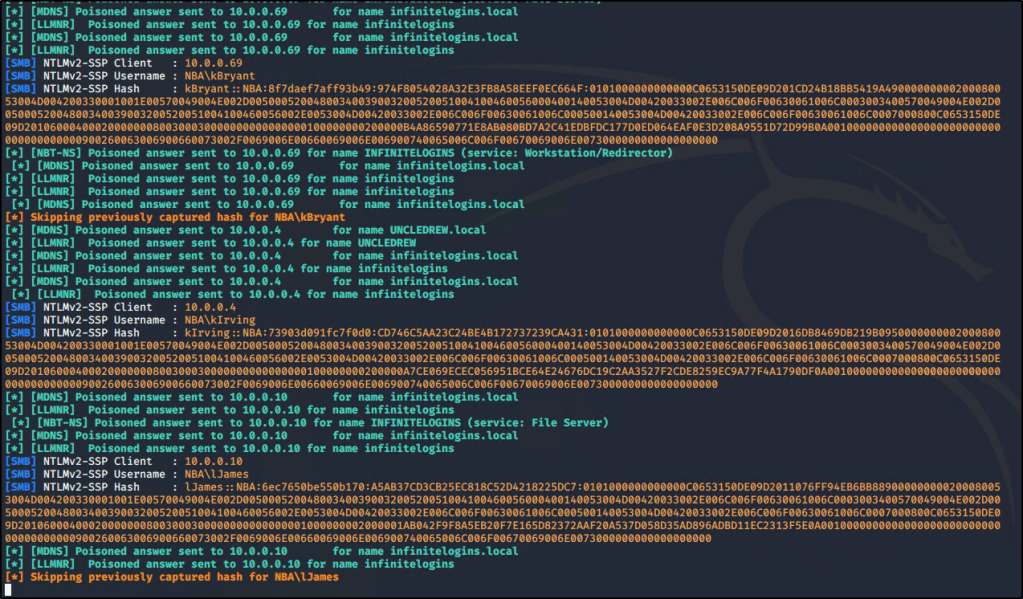
To start, let’s begin with setting the scenario up. In our fictional scenario, we’ll be targeting an Active Directory domain named NBA.local. Let’s begin by creating a handful of words that would be likely for this domain. We’re only going to start with a few words, as our list is going to grow exponentially when we start applying rules to them. In a real engagement, you may want to gather 10-20 words to use.
Here’s the list I started with.

We should also append the current year to the words. There are dozens of ways to do this, but a simple method is to use a for loop. for i in $(cat list1.txt);do echo $i;echo ${i}2020;echo ${i}2021;done > t

Now we’ll take this list, and feed it through Hashcat’s Best64 rule. hashcat --force <wordlist> -r /usr/share/hashcat/rules/best64.rule --stdout > hashcat_words.txt
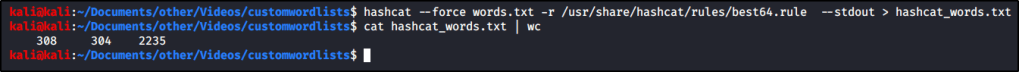
You can see from the screenshot that we turned our list that previously contained 4 words into a list that now contains 308 words! But if you look through the list, you’ll see it doesn’t contain any symbols. To fix this, we can create our own custom rule called append_exclamation.rule that contains the following:
:
$!

Now we can run hashcat again, but this time we’ll specify both rules instead of just the one. Just keep in mind that you may get duplicates, so you may want to also add the sort -u command.
hashcat --force <wordlist> -r append_exclamation.rule -r /usr/share/hashcat/rules/best64.rule --stdout | sort -u > hashcat_words.txt
This time when we check the number of words in the list, we see exactly double what we had before! This is because the list has the same 308 words as last time, but now also has them all with an exclamation added.

One of my favorite commands for creating wordlists: hashcat --force list.txt -r /usr/share/hashcat/rules/best64.rule -r /usr/share/hashcat/rules/toggles5.rule -r /usr/share/hashcat/rules/append_atsign.rule -r /usr/share/hashcat/rules/append_exclamation.rule --stdout | sort -u > list-uniq.txt
Hashcat Masking Attack
Some of my favorite masking attack commands to run:
hashcat -m 1000 -a 3 hashes\users.txt ?u?l?l?l?s?d?d?d?d
hashcat -m 1000 -a 3 hashes\users.txt ?u?l?l?l?l?s?d?d?d?d
hashcat -m 1000 -a 3 hashes\users.txt ?u?l?l?l?l?s?d?d
hashcat -m 1000 -a 3 hashes\users.txt ?u?l?l?l?s?d?d?d
hashcat -m 1000 -a 3 hashes\users.txt -1 ?u?l ?1?1?1?s?d?d?d?d
hashcat -m 1000 -a 3 hashes\users.txt -1 ?u?l ?1?1?1?1?s?d?d?d?d
hashcat -m 1000 -a 3 hashes\users.txt ?u?l?l?l?l?d?d?d?d
hashcat -m 1000 -a 3 hashes\users.txt ?u?l?l?l?l?l?d?d?d
hashcat -m 1000 -a 3 hashes\users.txt ?u?l?l?l?d?d?d?d
hashcat -m 1000 -a 3 hashes\users.txt ?u?l?l?l?l?d?d?d
hashcat -m 1000 -a 3 hashes\users.txt ?u?l?l?l?l?l?d?d
hashcat -m 1000 -a 3 hashes\users.txt ?u?l?l?l?l?l?l?d
hashcat -m 1000 -a 3 -1 ?u?l hashes\users.txt ?1?1?1?1?1?1?d?s
hashcat -m 1000 -a 3 -1 ?u?l hashes\users.txt ?1?1?1?l?d?d?d?d
hashcat -m 1000 -a 3 -1 ?u?l hashes\users.txt ?1?1?1?d?d?d?d?s
hashcat -m 1000 -a 3 -1 ?u?l hashes\users.txt ?1?1?1?d?d?d?d?s
hashcat -m 1000 -a 3 -1 ?u?l hashes\users.txt ?1?1?1?l?d?d?d?d?s
hashcat -m 1000 -a 3 -1 ?u?l hashes\users.txt ?1?1?1?l?d?d?s?s
hashcat -m 1000 -a 3 -1 ?u?l hashes\users.txt ?1?1?1?1?d?d?d?sUsing Rockyou2021 with OneRuleToRuleThemAll
There is a fantastic rule out there that you can get off Github. Combining this with Rockyou2021 has proved to have fantastic results. https://github.com/NotSoSecure/password_cracking_rules
.\hashcat.exe -m 1000 C:\hashcat\hashes\secrets.out E:\Wordlists\rockyou2021\rockyou2021.txt -r C:\hashcat\rules\OneRuleToRuleThemAll.rule -o cracked.txt